Online scams have become part of everyday life. They appear in text messages, social media posts, emails, and even phone calls that seem to come from legitimate companies. Many of these messages look convincing. They often include official logos, professional language, or urgent instructions. Yet most fraudulent schemes share a set of recognizable patterns.
Learning to spot those patterns early can save you time, stress, and money. The most reliable way to protect yourself is by understanding the scam warning signs that tend to appear before the trap fully reveals itself.
Criminals rarely rely on sophisticated hacking alone. Instead, many scams depend on psychology. Fraudsters study how people respond to fear, excitement, authority, and urgency. When a message pushes emotional buttons, people often react quickly instead of stopping to analyze the situation. This technique, known as social engineering, allows scammers to bypass careful thinking and trigger impulsive decisions.
Unexpected Messages From Strangers
One of the first red flags in many scams is a message that appears completely out of nowhere. It might arrive as an email, text message, or social media direct message from someone claiming to represent a company, bank, delivery service, or even a government agency. At first, the message may look normal. It could mention an account issue, a missed package delivery, or a reward you supposedly earned. However, the key detail is that you did not start the interaction. Legitimate organizations rarely request urgent action through unexpected messages, especially when sensitive information is involved.
Scammers rely on this tactic because it allows them to contact thousands of people quickly. Even if most recipients ignore the message, a small percentage may respond, which is often enough for the fraud to succeed. Unexpected contact works because it catches people off guard. If someone recently ordered a package or opened a new account, the message may feel believable. That moment of confusion can lead to quick decisions instead of careful thinking. Whenever a message appears unexpectedly, pause and verify it through official channels before responding.

Urgency is one of the most powerful psychological tools scammers use. Fraudulent messages often include phrases like “act immediately,” “your account will be suspended today,” or “this offer expires in one hour.” The goal is simple. Scammers want people to react quickly before they have time to think or verify the claim. When a message creates a sense of time pressure, the brain tends to switch into fast, emotional decision-making instead of slow, careful reasoning.
This tactic is especially common in messages pretending to come from banks, government agencies, or online services. A message may claim your account has been compromised and instruct you to click a link right away to secure it. In reality, legitimate organizations rarely demand instant action through random messages. They usually encourage customers to contact them through official websites or support channels. When a message insists that you must act immediately, treat it as a major red flag.
Offers That Sound Too Good to Be True
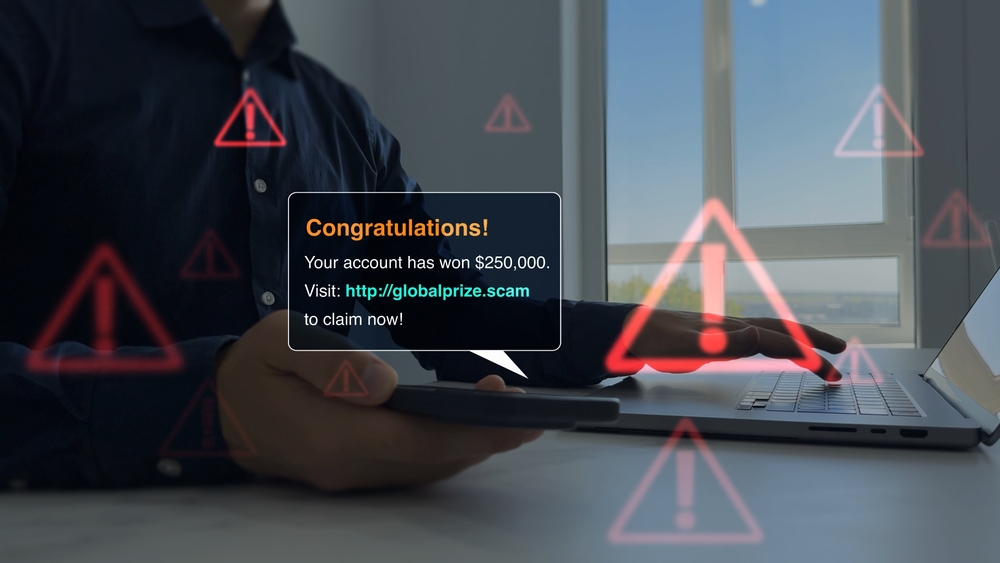
Another common scam warning sign involves offers that promise unusually large rewards. These messages may claim you have won a prize, qualified for a special investment opportunity, or been selected for a high-paying job that requires very little work. But legitimate opportunities rarely appear without clear details, verification processes, and realistic expectations.
Scammers rely on optimism to make these offers appealing. When people imagine gaining money or benefits quickly, they may overlook warning signs that would normally seem suspicious. Psychologists often call this optimism bias, the tendency to believe positive outcomes are more likely than they actually are. Investment scams frequently exploit this mindset by promising guaranteed profits or insider opportunities.
Requests for Personal or Financial Information
One of the clearest red flags of a scam appears when someone asks for sensitive personal information. This can include passwords, banking details, identification numbers, or security codes. Scammers often disguise these requests as routine account verification or security checks. A message might claim there is a problem with your account and ask you to confirm your details through a provided link. The website may even look identical to the real service, complete with logos and professional design.
The goal is to collect information that can be used for identity theft or financial fraud. This tactic works because people often trust messages that appear to come from official organizations. When a communication looks professional and includes familiar branding, it may trigger automatic trust. However, reputable companies almost never request passwords or sensitive financial details through email or text messages. If you receive a request for this type of information, treat it as a serious warning sign.
Messages That Contain Suspicious Links

Another common red flag appears when a message encourages you to click a link right away. These links may claim to lead to account verification pages, delivery tracking updates, or special offers. However, many scam messages rely on fake links designed to collect personal information or install malicious software.
These links often lead to websites that closely mimic real ones. The layout, colors, and logos may appear identical to official pages, which makes the deception harder to detect. Yet small details usually reveal the truth. The web address might contain misspellings, extra numbers, or unusual domain endings. Instead of directing you to a company’s official website, the link sends you to a fraudulent page controlled by scammers.
Payment Requests Using Unusual Methods

Scammers often insist on payment methods that are difficult to trace or reverse. They may ask victims to send money using gift cards, cryptocurrency, wire transfers, or peer-to-peer payment apps. Sometimes the message claims this unusual method is necessary to complete a transaction or resolve an urgent issue. This tactic works because these payment methods are fast and often irreversible. Once the money is sent, it becomes extremely difficult to recover. Scammers prefer these methods because they reduce the chance that victims can dispute the transaction later.
Fraudsters combine payment requests with urgency or fear. A message may claim that you owe taxes, fines, or fees that must be paid immediately. By creating pressure and offering a quick payment solution, scammers hope victims will comply without questioning the situation
Messages That Contain Spelling or Grammar Mistakes

Many scam messages contain noticeable spelling, grammar, or formatting errors. At first, this may seem like a small detail, but it can actually be an important clue. Legitimate companies usually review official communications carefully before sending them to customers. Messages filled with awkward phrasing or obvious mistakes often indicate that something is not quite right. Often, scammers operate internationally and write messages in languages that are not their first language, which can lead to unusual phrasing. People sometimes overlook these mistakes when the message triggers emotion or urgency. If a message claims there is a problem with your account, you may focus on the problem instead of the language used.
Requests to Keep the Situation Secret

Another troubling red flag appears when someone asks you to keep a situation confidential. Scammers may claim that sharing the information with others could jeopardize a deal, delay a reward, or create legal complications. In reality, this tactic is designed to isolate victims and prevent them from asking for advice. This tactic exploits trust and authority. When someone appears confident and knowledgeable, people may assume the secrecy request is legitimate. At the same time, secrecy prevents victims from hearing alternative perspectives that could expose the deception.
Stories That Constantly Change

Inconsistent information is another strong indicator of a scam. When scammers communicate with potential victims, their explanations may shift over time. Details about the situation, payment process, or identity of the sender may change slightly with each message. These inconsistencies often appear because the story is fabricated rather than based on real circumstances.
Scammers rely on momentum. Once victims become emotionally or financially invested, they may overlook inconsistencies because they want the situation to be legitimate. This is known as the sunk cost effect. People sometimes continue trusting a story simply because they have already invested time or effort.
Requests to Move the Conversation to Another Platform

Image credit: Shutterstock.
Another subtle red flag appears when someone insists on moving a conversation to a different platform. A scam might begin on social media, a dating app, or a job website. After a few messages, the person suggests continuing the conversation through private email, encrypted messaging apps, or text messages. While this request may seem harmless, it often serves a strategic purpose. Many online platforms monitor conversations for suspicious behavior and remove accounts linked to scams. By moving the conversation elsewhere, scammers avoid those safeguards and gain more control over the interaction.
This tactic builds a sense of personal connection. Once the conversation moves to a private space, the victim may feel they are communicating directly with a real individual rather than a stranger online. This shift can lower skepticism and make manipulation easier.
Emotional Stories Designed to Create Sympathy

Some scams rely heavily on emotional storytelling. The person contacting you may share a dramatic or heartbreaking situation. They might claim to be stranded abroad, facing medical emergencies, or dealing with unexpected financial hardship. The story often unfolds gradually, building trust before introducing a request for money or assistance.
This approach works because empathy is a powerful human instinct. When people feel compassion for someone in distress, they may focus on helping rather than questioning the situation. Scammers understand this psychological response and design their stories to trigger sympathy.
Romance scams frequently use this tactic. A scammer may spend weeks building an emotional connection before describing a sudden crisis that requires financial support. Because trust has already developed, victims may feel obligated to help.
Fake Websites That Look Nearly Identical to Real Ones

Many modern scams involve websites that imitate legitimate businesses. These pages are designed to look convincing, often copying the layout, colors, and branding of well-known companies. The site may appear completely authentic. However, closer inspection usually reveals small details that expose the fraud.
One common clue is the web address itself. Fake websites often include slight spelling differences, extra characters, or unusual domain endings. For example, a scam site might use a variation of a well-known company’s name while adding numbers or unfamiliar extensions. Scammers rely on visual familiarity to trick visitors. When people see a familiar logo or layout, they may assume the site is trustworthy and enter sensitive information without verifying the address.
Requests for Verification Codes or Security Numbers

Another major red flag appears when someone asks for verification codes or security numbers that were sent to your phone or email. These codes are typically part of two-factor authentication systems used by banks, email providers, and social media platforms. They are meant to confirm that the person accessing the account is the rightful owner.
Scammers sometimes trick victims into sharing these codes by pretending to be customer support agents or security representatives. They may claim they need the code to verify your identity or fix an account problem. In reality, the scammer is attempting to log into your account at the same time and needs the code to complete the process.
This tactic relies on authority and confusion. When someone sounds knowledgeable about security procedures, people may assume the request is legitimate. However, legitimate companies almost never ask customers to share authentication codes with anyone. If someone requests a security code you received privately, treat it as a serious warning sign.
Job Offers That Require Payment or Personal Details

Fake job opportunities are becoming increasingly common online. These scams often begin with messages offering remote work, flexible hours, or unusually high pay. The opportunity may appear on social media, job boards, or even professional networking platforms. The scammer may ask for an upfront payment for training materials, background checks, or equipment. In other cases, they may request personal information such as identification numbers or bank details before the job is confirmed.
This tactic works because people searching for work may feel hopeful or excited when a new opportunity appears. That optimism can make warning signs easier to overlook. Legitimate employers rarely require payment from applicants. They also conduct interviews through official channels rather than casual messaging apps. If a job offer requests money or sensitive information early in the process, it is wise to pause and verify the company through independent research.
Messages That Manipulate Trust or Fear

Some scams rely on building trust, while others use fear to force quick decisions. In many cases, scammers combine both strategies. The conversation might start friendly and supportive. The person may compliment you, show interest in your life, or offer help with something. Over time, this interaction can create a sense of familiarity, even though you have never met the person in real life. Once that trust develops, the scammer may introduce a sudden problem that requires money, personal information, or urgent action.
On the other hand, some scammers skip the trust-building stage and jump straight to intimidation. They may claim you owe taxes, face legal trouble, or risk losing access to important accounts. These messages are designed to create panic so that victims react quickly instead of thinking critically. Both tactics rely on emotional manipulation. Whether through trust or fear, scammers try to bypass logical thinking.
Read More: Scam Alert: 20+ Area Codes You Might Want to Ignore
Staying Alert Is Your Best Defense

Scams continue to evolve as technology and communication methods change. Fraudsters constantly test new strategies, from fake websites to emotional manipulation and impersonation tactics. However, despite these changes, most scams still rely on the same basic patterns. They use urgency, authority, excitement, or fear to encourage quick decisions without careful verification.
Learning to recognize common scam warning signs is one of the most effective ways to stay protected. Unexpected messages, unusual payment requests, emotional stories, and demands for sensitive information are all signals that something may not be legitimate. When several of these red flags appear together, the risk of a scam becomes even greater.
Fortunately, protecting yourself often requires only a few simple habits. Pause before responding to unexpected messages. Verify requests through official websites or customer service channels. Talk to trusted friends or professionals if something feels suspicious. Most importantly, remember that legitimate organizations rarely pressure people into immediate decisions. By slowing down and thinking critically, you can prevent scammers from exploiting emotional reactions.
If you would like to report a suspected scam to authorities, you can visit Internet Crime Complaint Center to make a report online.
A.I. Disclaimer: This article was created with AI assistance and edited by a human for accuracy and clarity.
Read More: The Invisible Scam: 15 Everyday Scams We Accept as ‘Normal’
Trending Products

Red Light Therapy for Body, 660nm 8...

M PAIN MANAGEMENT TECHNOLOGIES Red ...

Red Light Therapy for Body, Infrare...

Red Light Therapy Infrared Light Th...

Handheld Red Light Therapy with Sta...

Red Light Therapy Lamp 10-in-1 with...

Red Light Therapy for Face and Body...

Red Light Therapy Belt for Body, In...

Red Light Therapy for Shoulder Pain...

